HYCU recently announced the availability of HYCU for Azure, an on-demand data protection service for Microsoft Azure workloads. The offering extends the capabilities of HYCU to two of the three primary US-based cloud services, plus HCI on VMware and Nutanix environments.
Azure Support
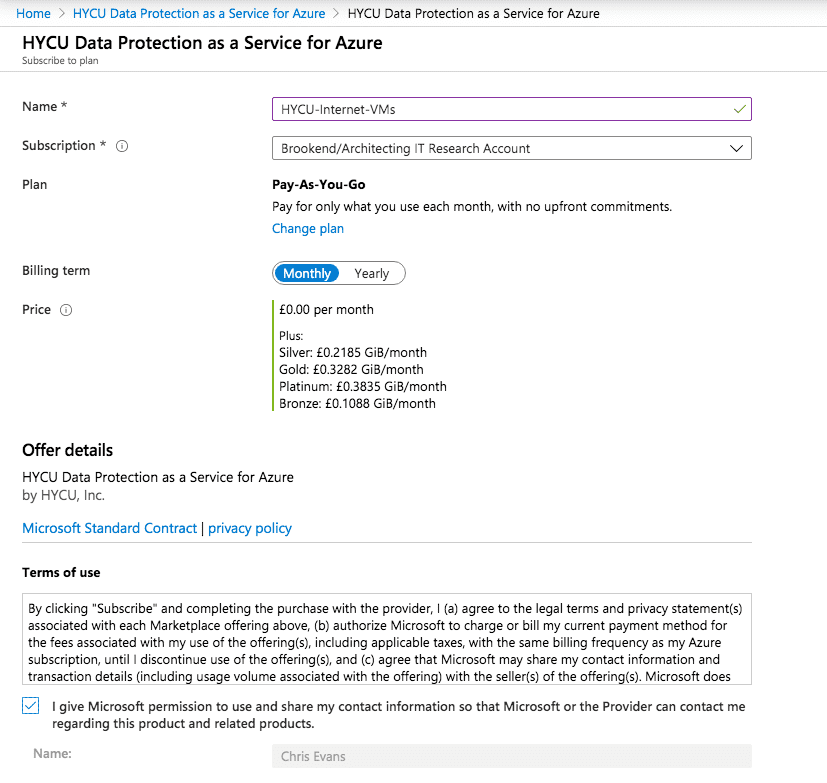
HYCU is now generally available through the Azure Marketplace. The solution is offered “as a service” which means charging by consumption. This method is effectively taking the storage capacity of all disks under protection, factoring in the frequency of backup throughout a standard period such as one month. There’s also an option to pay a fixed monthly subscription fee using what is described as a token-based plan.
- Validating HYCU Deployment by the Numbers
- Comtrade Software Becomes HYCU and Releases HYCU 3.0
- Automating HCI Data Protection
Service documentation reminds customers that HYCU only covers the cost of the software. There may also be additional charging for data stored in the customer’s storage account, plus any other temporary resources that are needed for backup and recovery (for example, temporary VM instances). As HYCU uses the customer’s storage account to store backup data, this makes sense.
Due to the impacts of COVID-19, at initial launch, HYCU for Azure is being offered free of charge for customers during the first three months (April, May & June 2020).
One crucial factor to note here is that billing is managed within the Azure account and appears as a line item on the monthly account bill. This process makes it simple to fire up a HYCU instance without having to engage in any sales discussion (see screenshot 1).
Protection
So, what resources can be protected and how exactly does the process of establishing data protection work? To find out, I created a test VM in my Architecting IT Azure research account. Once this was running a basic Apache web server, I subscribed to HYCU through the Azure marketplace. The subscription process requires activation of the service, then redirection to the HYCU website to set up a customer account. Once complete, I was returned to a HYCU sign-on screen and able to log into the HYCU portal using my Microsoft credentials.
Note that at this point, I’m logging into the HYCU portal, not a VM running in my account. This is true backup as a service, but with direct control over the backup data. From here, the process of discovering my VM and adding it to a policy followed the same steps as standard on-premises HYCU.
Standardisation
What have we gained by using a marketplace data protection solution? First, I’m using an interface and process that will already be familiar, if I’m a user of HYCU for Nutanix or VMware. This benefit means policy definitions can be consistent between on-premises and cloud environments.
- Data Protection Choices for Heterogeneous Environments
- Nutanix Mine Puts Backup Software Vendors on a Level Playing Field
- Briefing Document: HYCU
Second, I have control over the backup data and can choose how to re-use that content, including migration to other Azure accounts or to use as part of a migration process. HYCU Protégé provides the capability to link up multiple data protection instances and implement centralised data protection monitoring/management, disaster recovery and application mobility. We’ll cover that in a separate discussion.
Applications
There’s one area not currently aligned between HYCU on-premises and in Azure, and that’s full support for applications. In the public cloud, application protection could mean two things; applications running within virtual instances and native apps (like Azure SQL). Through consistent snapshots, HYCU for Azure currently supports application protection within virtual instances. This feature isn’t currently surfaced to a dashboard icon, but I’m assured it’s on the way.
Support for native applications depends on the interfaces offered by the cloud provider. I feel that this is an area in which we’re likely to see slow progress, as the development of these APIs will be heavily dependent on how cloud vendors implement their database technologies. This may not be an area they want to expose too readily.
Scratching the Surface
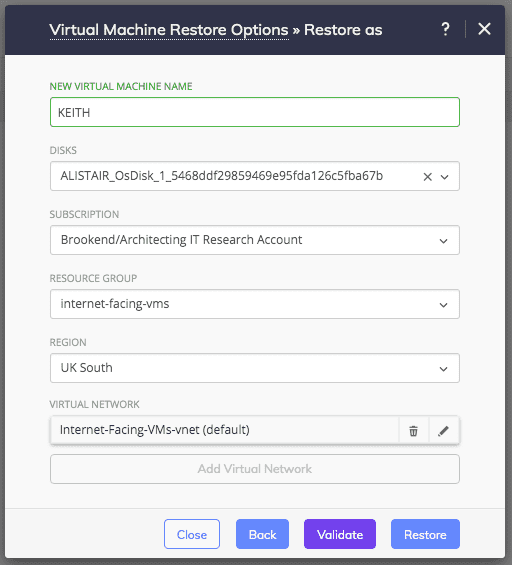
There’s so much more to investigate within the HYCU interface. For example, security is integrated with Microsoft Azure credentials, which should provide for multi-tenanted deployments and dedicated backup operators (protection sets). Restores can be file-based or an entire VM (see screenshot 3, which is the process for restoring ALISTAIR (test machine), as a new VM called KEITH). I’m keen to see what degree of automation is put in place. Of course, this is the first release of the offerings, so new features will drop in over time.
The Architect’s View
Data protection needs to be consistent across platforms. This requirement means implementing standardisation around policies, data formats and APIs. These are all topics we’ve covered previously. Native data protection currently provides significant lock-in to a single platform. This restriction isn’t inherently wrong – unless you want to migrate applications to a new platform and retain access to historical backups.
HYCU is making significant progress towards unified data protection across all platforms. When can we expect AWS? I don’t know, but I’m sure it will be in future plans. I’ll also be looking out for integrations into native applications. In the coming months, we’ll be doing some more hands-on with HYCU and Protégé, bringing some practical realism to the blog conversations over the past two years. Hopefully, this post has provided a little taster of what to expect.
Copyright (c) 2007-2020 Brookend Limited. No reproduction without permission in part or whole. Post #1e0f. Disclaimer: HYCU is a client of Brookend Ltd.